Many people assume that infections with malware are the result of obvious mistakes: installing suspicious software, opening malicious attachments in an email, or clicking on the wrong link. A common belief is that by being careful, one can simply avoid these situations. That’s true for the vast majority of attacks. Unfortunately, advanced cyberattacks do not always adhere to this rule.
Some of the most powerful attacks today come with no warning signs, require no suspicious downloads, and sometimes not even a single click or interaction from the victim. These attacks rely on so-called zero-day vulnerabilities, and in the most dangerous cases, zero-click exploits.
Understanding these concepts helps us understand why storing the private keys to your Bitcoin wallet on everyday devices such as laptops or smartphones carries inherent risks — and why hardware wallets exist in the first place. Let’s take a closer look.
What is a zero-day vulnerability?
A zero-day vulnerability is a security flaw in software that is unknown to the developers responsible for fixing it. The name comes from the simple fact that the developers have had zero days to release an update.
As long as such a vulnerability remains undiscovered by the developer, attackers who know about it can exploit it freely and at any time they choose, making it a very powerful weapon. These flaws can appear in almost any kind of software, including operating systems, browsers, messaging apps, or the countless libraries and system components they depend on.

Modern software can get incredibly complex. Operating systems alone consist of tens of millions of lines of code interacting with thousands of hardware components and external programs. Even with extensive security audits and testing, it is unrealistic to expect that every possible bug can be found before attackers do.
Occasionally, a zero-day may allow malicious actors to execute code on a device, gain elevated privileges, or access sensitive information. When attackers discover such a flaw first, they effectively gain a temporary advantage. Until the vulnerability becomes public and a patch is released, every device running the affected software may be exposed.
What also matters here is that the finder of an exploit does not have to end up being the one using it. There is an entire market for zero-days, with brokers and commercial surveillance vendors buying and selling them for enormous amounts of money. That makes them particularly attractive for state-level actors, intelligence services, and attackers targeting especially valuable individuals. So while zero-days may sound exotic, they are not just rare outliers, but an established option in the toolchain of advanced attackers.
Zero clicks, zero chance
A zero-click exploit often builds on top of zero-day vulnerabilities, making them one of the most potent tools at an attacker’s disposal. Normally, malware requires some form of interaction from the victim – opening a file, clicking a link, or installing an application. With a zero-click exploit, as the rather obvious name suggests, no interaction is required at all.
The attacker only needs to send specially crafted data to the target device. When the device processes that data, the vulnerability is already triggered. In practice, these attacks often target components that process incoming content automatically. Messaging apps, email clients, image and video decoders, push notification systems, and network protocols have all been used as attack surfaces in the past.
Imagine receiving a push notification on your phone. At this point, the app and the operating system must have already processed the associated data in one way or another – otherwise the notification couldn’t even exist. If that data somehow exploits a bug, malicious code may execute before the user even looks at the message…
Pegasus
One of the most well-known examples of this type of attack is the Pegasus spyware developed by the NSO Group. Pegasus has been used in several documented campaigns targeting journalists, activists, and political figures. In multiple cases, researchers discovered that the spyware was installed through zero-click vulnerabilities in Apple iMessage.
The attack worked by sending specially crafted messages that triggered bugs in how iOS processed certain types of content. Because iMessage automatically parses incoming messages in the background – for example to generate previews – the malicious payload could execute without the user opening the message or interacting with the device at all.
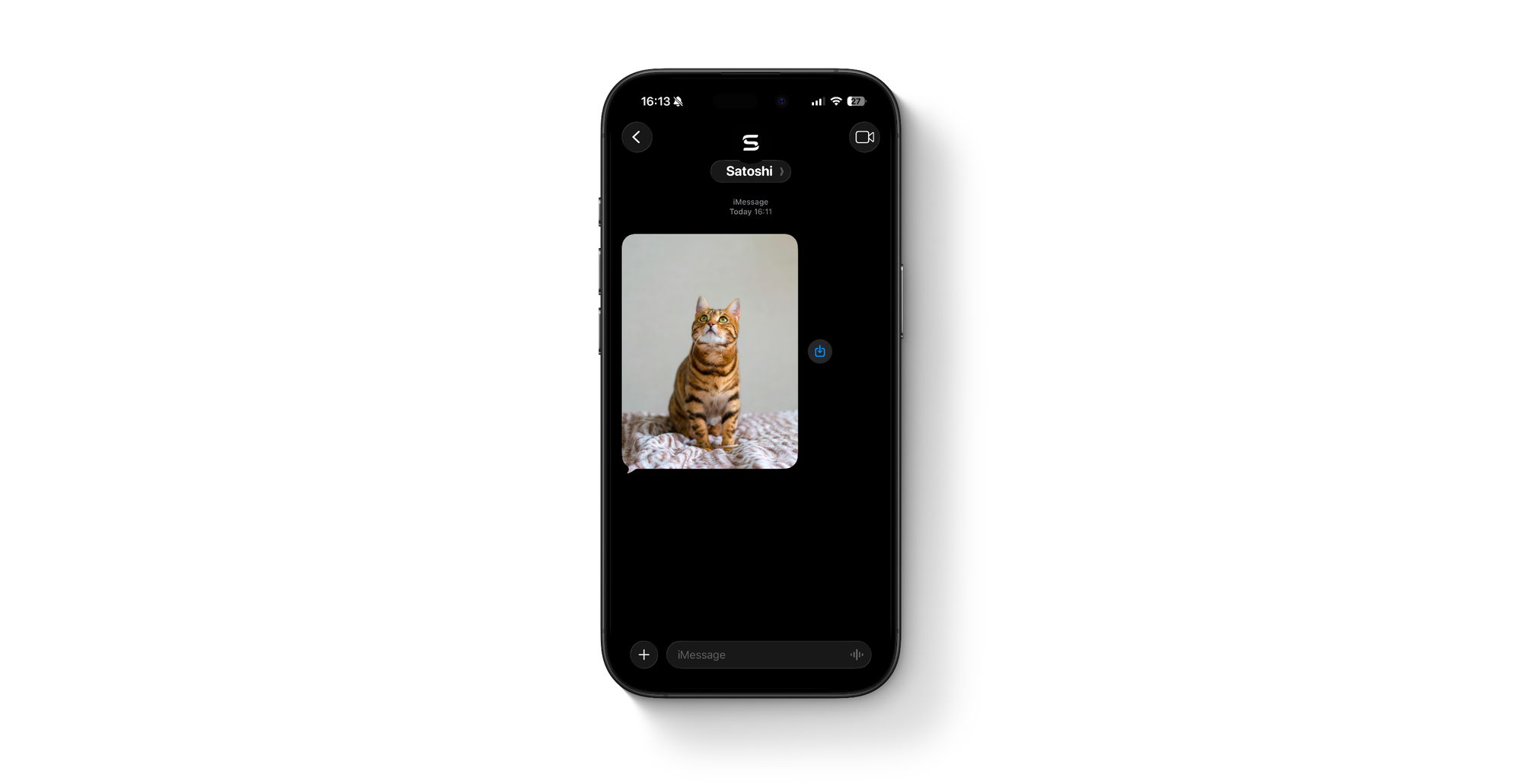
Once the exploit succeeded, the spyware could gain deep access to the phone, allowing attackers to read messages, access files, activate microphones, and track the device. Even more striking was the fact that many victims never noticed anything unusual happening on their devices. The compromise occurred silently in the background.
While such sophisticated attacks are typically used in high-profile surveillance operations, they illustrate an important point: even well maintained devices that are widely considered secure can contain unknown vulnerabilities – and you can never know for sure.
Even experts are vulnerable
When discussing security, it’s common to hear statements like: “I would never install malware by accident.” Being careful with downloads and suspicious links is certainly good practice. However, more advanced exploits like in the previous section can fundamentally change the situation.
If an attacker exploits an unknown vulnerability in your operating system, browser, or messaging app, your personal security habits may not matter as much. Even security professionals and cybersecurity companies have fallen victim to such attacks. The uncomfortable reality is simple: no device connected to the internet can be assumed to be secure.
Keeping systems updated and avoiding reckless behavior can of course help to reduce many common threats. But when it comes to zero-day vulnerabilities, keeping your system updated won’t help – for obvious reasons.
Hot wallets and exchanges as targets
If an attacker manages to compromise a device, the next step is naturally to search for valuable information. In the context of cryptocurrencies, this generally means looking for private keys stored in software wallets or trying to obtain sensitive information from the user, e.g. to log into their exchange account.
Hot wallets store the keys to access funds directly on your smartphones or laptop. If malware gains sufficient access to the system, it may be able to read wallet files, monitor memory for sensitive data, or intercept transactions.
This is not just a theoretical risk. Over the past years, multiple malware campaigns have specifically targeted cryptocurrency wallets by scanning infected systems for wallet files and private keys. In other cases, attackers have been able to compromise the wallet software itself.
And this brings us back to the core danger of zero-day and zero-click exploits: if the device itself has an inherent weak point, then the user does not necessarily need to make a mistake. A previously unknown vulnerability may be enough to give an attacker the foothold they need – and with that, the coins they want.
The goal here is not to instill fear by making alarmist references to zero-click vulnerabilities. It’s to illustrate the simple fact that smartphones and desktop computers are not safe environments for Bitcoin wallets.
The hardware wallet pitch
You guessed it, hardware wallets like the BitBox were designed to address exactly this problem. Instead of storing private keys on a general-purpose computer or smartphone, a hardware wallet keeps them inside a dedicated device built specifically for secure key management.
The device signs transactions internally after the user’s direct confirmation, and the private keys never leave the secure and transparent environment of the hardware wallet. The host computer merely acts as a communication interface with the Bitcoin network.
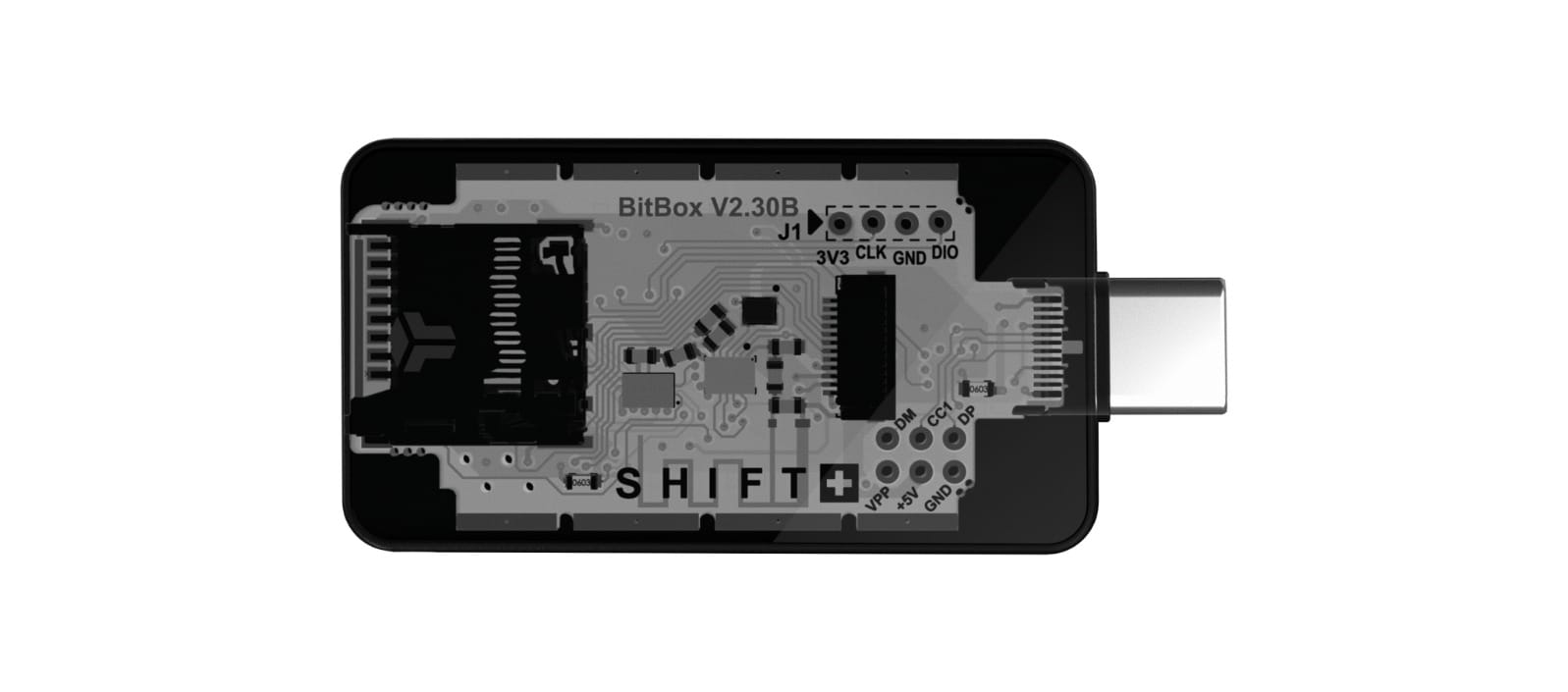
You should not have to fully trust your everyday devices. Computers and smartphones run complex operating systems and countless applications, making them far more likely to contain vulnerabilities.
Hardware wallets assume that the computer they are connected to might be compromised from the very start and therefore isolate their most critical secret – the private keys – from it. The display of a hardware wallet meanwhile serves as a source of truth when verifying transaction details or receive addresses, since it establishes a direct line of communication with the user, without relying on the host device.
Conclusion
No security system can offer absolute protection, and you should not trust anyone who claims otherwise. However, reducing trust placed in complex operating systems can significantly improve resilience against attacks. Zero-day vulnerabilities and zero-click exploits illustrate an important reality of cybersecurity: human error is not always the issue.
A hardware wallet introduces a clear separation between two environments: the internet-connected device you use every day, and the isolated device responsible for protecting your private keys.
Even if a computer or smartphone becomes compromised through a zero-day exploit, the attacker still faces a major obstacle. The private keys remain inside the hardware wallet, and transactions must still be confirmed on the device itself.
In other words, the attacker may control the computer — but they do not control your coins.
Don’t own a BitBox yet?
Keeping your crypto secure doesn't have to be hard. The BitBox hardware wallets store the private keys for your cryptocurrencies offline. So you can manage your coins safely.
Both the BitBox02 Nova and the BitBox02 also come in a Bitcoin-only edition, featuring a radically focused firmware: less code means less attack surface, which further improves your security when only storing bitcoin.
Buy the BitBox02 Nova or grab a BitBox02 in our shop!

Shift Crypto is a privately-held company based in Zurich, Switzerland. Our team of Bitcoin contributors, crypto experts, and security engineers builds products that enable customers to enjoy a stress-free journey from novice to mastery level of cryptocurrency management. The BitBox02, our second generation hardware wallet, lets users store, protect, and transact Bitcoin and other cryptocurrencies with ease — along with its software companion, the BitBoxApp!